The NIS2 Directive (EU 2022/2555) is a cybersecurity directive adopted by the European Union in December 2022. Its objective is to sustainably increase the level of cybersecurity across the EU. It requires EU member states to transpose binding requirements for network and information security into national law by October 17, 2024, at the latest.
These include comprehensive requirements relating to:
- the state of the art of technical and organizational IT security measures,
- mandatory reporting of IT security incidents,
- risk management and governance at management level,
- regulatory supervision, audits, and enforcement measures, as well as
- sanctions for non-compliance.
With this, NIS2 pursues the overarching goal of sustainably strengthening the cyber resilience of critical infrastructures and essential services in Europe, and of better protecting the EU against cyberattacks, IT disruptions, and systemic risks.
In Germany, the new “Act to Implement the NIS2 Directive” entered into force on December 6, 2025, thereby reforming cybersecurity law. In Austria, the draft legislation (NISG 2026) was adopted by the National Council in December 2025 and will enter into force on October 1, 2026.
Network security has taken on a new heightened importance in the European Union (EU): The European Network and Information Security Directive (NIS for short) obliges EU states to establish stricter, uniform cybersecurity standards for their system-relevant companies and institutions.
The NIS2 directive, published in December 2022, is the logical response to the dramatically changed cyber risks since the first NIS directive was issued in 2016. In its latest situation report, for example, the German Federal Office for Information Security (BSI) estimates that the threat situation is higher than ever before. By 2024, critical infrastructures in the EU should therefore be more resilient and responsive through designated cybersecurity institutions, strategies, and cooperations.
This article informs you about the specific requirements associated with NIS2, the areas they apply to, and how LANCOM supports you in implementing them quickly and securely.
NIS2 in a nutshell
The term “NIS” stands for “Network and Information Security.” The NIS2 Directive is the successor to the first NIS Directive (NIS1) from 2016 and significantly expands its scope of application, requirements, and enforcement mechanisms.
To whom does the NIS2 directive apply?
The aim of the NIS guidelines is to equip system-relevant private and public sectors of the EU states with appropriate security technology and to improve the cooperative exchange of information on the subject of network security between the member states. NIS2 defines even clearer identification criteria for belonging to critical infrastructures according to the European Programme for Critical Infrastructure Protection (EPCIP) and includes new sectors:
Additional EPCIP sectors since NIS2 (2022)
- Production & processing (among others food, medical products, chemicals, vehicals, electronics, machinery)
- Providers of publicly available electronic communications services
- ICT service management (information and communication technologies, ICT in short)
- Public administration
- Space
- Postal and courier services
- Waste and waste water management
- Research
So who is affected by NIS2?
All mid-size and large organizations operating in the sectors listed above, as well as companies that meet the specified criteria, will be covered by the new NIS2 directive.
As a result, a very large number of medium-sized enterprises are now obliged to observe the security measures laid down in the directive and are subject to certain reporting obligations.
What companies should bear in mind about NIS2
Many companies will be newly affected by NIS2.
For example, providers of public electronic networks and communications services, manufacturers of data processing equipment, electronic, and optical products, and managers of information and communications technologies will all come under closer scrutiny under the new directive. This also includes system vendors and other technical suppliers. So, what now?
This is a lawyer providing clear answers on the impact of NIS2:
The NIS2 directive addresses current cybersecurity threats by recognizing the impact of compromised or incapacitated organizations in a wider range of sectors, and makes these organizations accountable for a required level of information security. It also establishes a European information and network security communication and cooperation network, EU-CyCLONe.

"Directive (EU) 2016/1148 of the European Parliament and the Council aimed to build cybersecurity capabilities across the Union, mitigate threats to network and information systems used to provide essential services in key sectors and ensure the continuity of such services when facing incidents, thus contributing to the Union’s security and to the effective functioning of its economy and society."
Directive (EU) 2022/2555 of the European parliament and of the council of 14 December 2022
Coordinated risk and crisis management
Specifically, the NIS2 directive serves as a "coordinated cybersecurity framework." It calls for national cybersecurity strategies and responsible authorities, e.g. as secure, central contact points, constantly available computer security incident response teams (CSIRTs), and risk and crisis management officers.
Compared to NIS1 the tasks that these authorities fulfill are more precisely defined, as are the components the network security strategy should consist of, e.g. security of the supply chain, secure communication, use of encryption and access controls, emergency communication systems, and more (see legal info paper).

Tighter enforcement
Clear regulations are in place for monitoring and reporting. The European Union Agency for Cybersecurity (ENISA) shall keep a register of digital infrastructure companies covered by the directive. Security incidents must be reported within 24 hours and analyzed in a final report after a month at the latest. Every two years, the state of cybersecurity in the EU will be reviewed and assessed.
The institutions affected by NIS2 must prove that they comply with the relevant network security concepts by means of various versions of due diligence and proof of implementation (more on this in the legal info paper). In the event of violations, fines of up to EUR 10 million or 2 percent of the previous year’s worldwide turnover are to be expected.

The best way for companies to prepare for NIS2
Small and medium-sized companies should take heed when it comes to NIS2: Manufacturing and processing industries in diverse sectors now have to take care of their network security just as much as large corporations. Whether the food or automotive industry, or manufacturers, processors, or distributors of medical, electronic, or chemical products – many companies must now reassess their network security and adapt it if necessary.
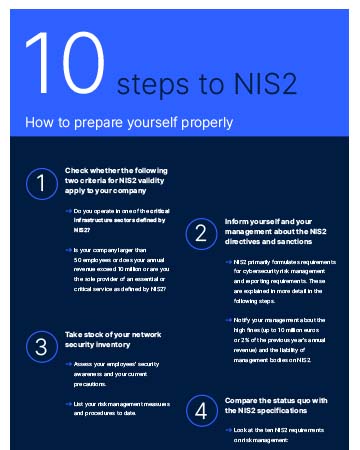
How best to prepare for the new laws that implement NIS2? Our infographic shows you how you can start a spring-clean of your IT security today.
Hands-on tips for NIS2 directive implementation: What you can do now
The NIS2 directive primarily outlines national network security strategies and professional risk management. But what does that mean for you? And how can a network technology supplier like LANCOM help you?
First of all, each government of the EU member states has to lay down the legal framework in national law for their own country. By observing the following items, you will be well prepared for the national guidelines based on NIS2.
Make precautionary arrangements
It's best to start now by reviewing and critically examining your current cybersecurity status. How sensitive and critical is the data you work with and are the services you provide? How serious would a system shutdown or outage be for your operations?
If you rate both of these highly, your network needs to be adequately protected. This starts with your technical equipment with secure, European gateways and firewalls and leads on to good risk management.
Conduct professional risk management
The first task in effective risk management is to clearly define responsibilities: Who is in charge of protecting the network and to what extent – the in-house IT, a special security team, or an external service provider? What risks are relevant for you, and how do you protect yourself against them?
Clear regulations help to deal with security incidents and to keep operations running even in a crisis. Network security ranges from employee training, a secure supply chain, tested network components, systems, and services, and cyber hygiene procedures, over the use of encryption, access controls, and authentication, to secure voice, video, and text communications, and much more.

Hands-on tip:
You can immediately upgrade the security of your existing devices without much extra effort. We'll show you exactly how here. We have also got more hands-on tips to help you build a solid security foundation.
You can also read our white paper on how to gain network visibility using deep packet inspection and encryption proxies:
Whitepaper: Network visibility through DPI and encryption proxies
Ensure ability to (re)act
If something should go wrong despite all the precautions, damage limitation is ensured by emergency teams and procedures. Your network security emergency response team should be available at all times, have redundant communication channels, and be in a secure location.
Regular situation assessments and proactive vulnerability analysis help them to monitor your network around the clock, detect threats early, and inform you immediately in the event of a security incident.

Hands-on tip:
Cloud-based network management increases your network security and reduces the load on security managers. The network management cloud takes over essential monitoring tasks and simplifies the configuration of your firewalls and other devices. A well-coordinated Security Information and Event Management (SIEM) system is worth its weight in gold here. Take a look for yourself: Cloud-managed security!
Ensure recovery from security incidents
After an IT security incident, every effort is made to recover from the crisis. But even before a crisis happens, what you need is a mature concept for data protection and digital sovereignty.
A major step has been taken once you have data backups and geo-redundant cloud servers. In the best case scenario, you will have in-house capabilities to close any security gaps and maintain the security of your systems.

Hands-on tip:
Test your digital sovereignty with our index and find out about the relevance of data sovereignty!
Or you can get familiar with our tips for digitally sovereign companies and authorities.
Count on good cooperation and support
While the prevention, resolution, and recovery from incidents is one thing, having the experts and resources to do so is another. NIS2 requires security precautions throughout the acquisition, development, maintenance, and management of networking and information systems. But not every company has the capacity for its own cybersecurity team.
In-house IT or experienced employees often have to manage network security and tasks such as firewall configurations in addition to their other duties. In cases like these, life can be a lot easier if you can rely on the right support.

Hands-on tip:
Let your UTM firewall do most of the work! With a user-friendly web interface as the central management console in the browser, the LANCOM R&S®Unified Firewalls provide a comprehensive overview of all devices and connections in the network, making it considerably easier to implement security requirements.
In addition, we support you with numerous support and training offerings as well as helpful reference projects for orientation and information:
Customer reference: Security package for practices with Hasomed
Conclusion: The new EU NIS2 directive affects significantly more companies and institutions than its predecessor NIS1. It has more stringent specifications, a more clearly defined verification of their implementation, and stricter sanctions in case of non-compliance.
Especially industries in food processing, manufacturing, providers of public electronic network and communication services, and administrators of information and communication technologies need to check whether the new guidelines apply to them and to monitor how their country is implementing the EU's requirements into national law.
Ideally, you should get ready now and subject your network security to a critical check-up. LANCOM Systems can help you with this – with the right technical equipment, security solutions tailored to your needs, and the necessary know-how.
Ask the AI chatbot!
Do you still have questions? Or maybe you cannot find the information you are looking for? The AI-based Digital Assistant will answer all your questions about network security, IT security, and LANCOM R&S®Unified Firewalls – at any time, quickly, and without searching! Alternatively, you can of course still use the contact form.