Firewall features
The digitized present and sophisticated cyber attacks redefine the rules for your network security. Application control and blocking as well as intrusion detection and prevention are therefore a must-have for secure IT networks. Integrated in the powerful firewall operating system LCOS FX, these and other industry-leading UTM security features ensure a trustworthy IT infrastructure "Engineered in Germany" and a significant security advantage for your network. The feature set for the LANCOM R&S®Unified Firewalls and LANCOM vFirewalls is regularly expanded so that professional networks are also protected against new types of risks.
- Application Management & R&S®PACE 2 DPI engine
- Intrusion Detection / Prevention System (IDS / IPS)
- Anti-Virus / Anti-Malware / Anti-Spam
- Docker container management for secure edge computing
- VPN: IPSec VPN, SSL VPN, and WireGuard
- Secure Web Gateway (SWG) using HTTP(S) proxy
- DNS Web Filter & Content Filter
Unified Threat Management (UTM) combines multiple security functions into a holistic security package. This coordinated feature set facilitates the implementation and management of professional security strategies. The LCOS FX operating system offers, among other things, the following firewall security features for the LANCOM R&S®Unified Firewalls and LANCOM vFirewalls.
Notes:
* A Full license is required to use all UTM features.
** A SAG Basic/Full license (Secure Application Gateway) is required to use the Docker container functionality.
Application Management & R&S®PACE 2 DPI engine*
DPI-based control of applications and content
Monitoring digital applications and precisely classifying network traffic at the application level are just two of the many tasks performed by a Deep Packet Inspection (DPI) engine. The industry-leading R&S®PACE 2 DPI engine inspects data packets down to layer 7 – in other words, it analyzes not only the metadata but also the data area of a…
Intrusion Detection / Prevention System (IDS / IPS)*
Database-based protection against known threats
Known threats such as DDoS (Distributed Denial of Service), portscans, or botnets must also be taken seriously. To do this, the Intrusion Detection / Prevention System ("IDS / IPS") maintains a database of known threats to reliably protect end devices in the network from a wide range of hostile attacks. Included in the threat database…
Anti-Virus / Anti-Malware / Anti-Spam*
Protection against unknown threats with sandboxing and machine learning
To protect networks against cyber attacks on previously unknown vulnerabilities ("zero-day exploits"), a multi-stage scanning concept detects and eliminates potential threats. To do so, cloud-based sandboxing and machine learning (ML) are used after a local scan. Machine…
Docker container management for secure edge computing**
Secure data processing at the network edge
The integration of Docker containers enables fast and isolated deployment of applications directly on LANCOM R&S®Unified Firewalls and vFirewalls. This creates a secure, flexible platform for secure edge computing: workloads run locally, in real time, and fully protected by…
VPN: IPSec VPN, SSL VPN, and WireGuard
Secure and encrypted site networking
Company locations, such as branch offices or mobile employees in home offices, are securely connected via a virtual and private network (VPN). The client-configurable VPN acts like a secure data tunnel, although it uses the public Internet as a communication path. This creates a…
Secure Web Gateway (SWG) using HTTP(S) proxy*
Filtering network traffic
A Secure Web Gateway (SWG) is used to protect a network and their devices against access from the Internet. This is precisely the task performed by the HTTP(S) proxy server in the Unified Firewalls, which analyzes and filters network traffic down to the application level. The proxy acts as a barrier between the user's own network and…
DNS Web Filter
& Content Filter*
Content-based filters to protect against phishing attacks
The use of user-owned devices (BYOD) is no longer a novelty in schools or in hybrid work environments. The DNS Web Filter provides security without the need for certificates: Using an online scanning technology, DNS queries that pass through the DNS server of your Unified Firewalls are identified, classified, and filtered according…
SD-WAN with dynamic routing & Traffic Shaping
Efficient and robust site networking
By efficiently controlling the maximum bandwidth as well as the line prioritizing (Traffic Shaping), the applications that are important to you are guaranteed to run with the best quality in and out of your network. Pre-configuration of common scenarios as well as selectable Traffic Shaping groups and profiles (QoS) depending on the WAN…
Network segmentation (VLAN)
User-based rules and network separation
The logical division of a network allows you to define individual security settings and access rights depending on the requirements of the user groups and to divide your infrastructures and applications into different areas. This separation (zoning) does not create classic physical networks, but purely logical virtual networks, so-called VLANs…
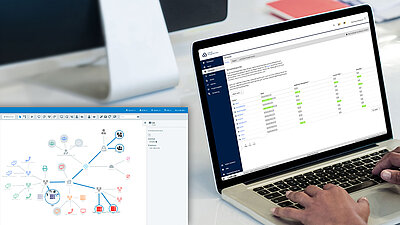
Management, monitoring & administration
Despite progressive automation, an "easy-to-use" operating concept is more than helpful. In order to reduce complexity and thus susceptibility to errors, the following tools and functions are available for the Unified Firewalls:
- Management tools with graphical interfaces,…
User authentication
Policy compliance thanks to access rules
Network access control is indispensable to ensure that you always have an overview of which users, devices, and services are in the network, which identity is really behind them and who has which functions or is allowed to perform which actions. Authentication for policy compliance via web or client can be…
Cloud-managed Security
Management via the LANCOM Management Cloud (LMC)
The LMC automates and simplifies the management, configuration, and monitoring of your Unified Firewalls. For example, you can use the central management instance to administer Application Management and firmware updates. The automatic setup of VPN connections between all sites (Auto-VPN) is just as easy as the integration of new firewalls via a secure pairing process as well as the replacement of firewalls including complete configuration.
Backup & restore
Automatic or scheduled backups
Backups of your data are necessary to protect it from corruption and deletion. Especially complex firewall configurations should be backed up before significant changes or a firmware upgrade. Backups can be automatic or scheduled and controlled via local or remote access or imported automatically during an installation. In addition, the backups can be automatically uploaded (FTP, SCP) or saved to a USB stick in case of a disaster recovery.
SSL Inspection
Security even for encrypted channels
The increasing encryption of data traffic leads to a growing risk of malware infiltrating systems through encrypted channels. With Secure Sockets Layer Inspection, or SSL Inspection for short, Unified Firewalls offer the ability to perform scanning, filtering, and application detection even on encrypted data packets to successfully implement your security requirements.
High availability (HA)
Increased reliability of your Unified Firewalls
For trouble-free operation, high availability is a necessity in critical network installations. Therefore, multiple Unified Firewalls in a HA cluster ensure increased reliability and constant availability. Thanks to the active / passive cluster, the second firewall of the same model only steps in when it is really needed. Hot…
Licenses
A valid license is required to operate a LANCOM R&S® Unified Firewall or LANCOM vFirewall. The flexible licensing model lets you choose both your preferred feature set (four variants) and the license duration (1, 3, or 5 years, or monthly billing with an existing SPLA contract). To help you select the right option for your needs, here is a brief overview and detailed information in the firewall data sheets.
|
Basic |
SAG Basic |
Full |
SAG Full |
|
|---|---|---|---|---|
|
Activation of firewall functionality (incl. user management, backups, network segmentation, VPN) |
|
|
|
|
|
Firmware releases and updates |
|
|
|
|
|
Manufacturer support * |
|
|
|
|
|
Complete UTM functions (incl. application control, attack prevention, protection against viruses, malware, and spam, youth protection, phishing defense) |
– |
– |
|
|
|
Integration of OCI Docker containers |
– |
|
– |
|
Firewall license portal
Always keep a clear overview of the status of your firewall licenses: In the myLANCOM Firewall License Portal, you can monitor, activate and renew your firewall licenses all securely in one place and decide for yourself which of your employees will be granted access to the portal.
When choosing the right firewall, both the amount of data traffic and the size of the company are decisive factors. With the LANCOM R&S®Unified Firewalls and the virtual variants of the LANCOM vFirewalls, you are ideally equipped for any application – and without compromising on security functions, because the maximum security of your network is guaranteed at all times by Unified Threat Management (UTM).