What is Unified Threat Management?
UTM stands for Unified Threat Management and combines numerous security functions such as anti-virus and SSL inspection in a unified security solution on a shared platform. In practice this means: Instead of setting up individual security mechanisms in different systems, a “next-generation” UTM firewall is a single device that provides a uniform operating concept for the implementation of customized security guidelines.
Current network security and Digital Sovereignty according to NIS2 specifications
Network security is constantly evolving and must address new challenges. The EU NIS2 Directive on network and information security now meets this need by establishing clear specifications and sanctions to enhance cybersecurity in EU companies. A positive side effect is that Digital Sovereignty also strengthens with increased security. Are you affected? If so, what does this mean for your company? Take the NIS2 check and learn more on our topic pages.
More about NIS2 and Digital Sovereignty
What makes Unified Threat Management (UTM) worthwhile?
An average of 394,000 new malware variants are created every day (“BSI Lagebericht 2021”). But not only is the number of malware variants increasing dramatically, the quality of the attacks is also “improving”. Emotet was a particularly aggressive form of a ransomware attack, with cyber criminals encrypting the data and systems of companies and public institutions in order to extort funds. As a proactive counter to these existence-threatening scenarios, an investment in a next-generation firewall with Unified Threat Management (UTM) is more than worthwhile.

What is a UTM firewall?
A UTM firewall is an all-in-one solution that combines various security functions in a single system:
- Protects the network against viruses, malware, spyware, or encrypted e-mail attachments with malicious content
- Protects against attempted attacks even before they enter the network
- Protects against access to undesired Internet content from within your network
- Protects against novel, zero-day threats
- Protects against unauthorized access to sensitive company data by means of network segmentation
- Protects against the operation of unwanted services
- Protects against spam
Cyber Security reimagined
„Cyberattacks are omnipresent and constitute a huge threat to the entire economy, regardless of size or industry. The rapid increase in mobile work and cloud services is also making companies even more vulnerable to cyberattacks. While greater flexibility is achieved through remote work and cloud services, the new structures, at the same time, create new attack vectors for cybercriminals which should sound the alarm bells with IT security experts.“ – techconsult study from 2022
SIEM integration service for cloud-managed LANCOM R&S®Unified Firewalls
Robust security management is essential, especially for larger organizations and managed service providers (MSPs). A centralized Security Information and Event Management (SIEM) system helps organizations detect, analyze, and respond to security threats quickly.
We invite you to enhance your SIEM with our integration service for cloud-managed LANCOM R&S®Unified Firewalls, ensuring comprehensive detection of attacks on your network infrastructure. Further information about technical prerequisites and setup can be found here:

How does Unified Threat Management work in detail?
The following mechanisms are used in Unified Threat Management firewalls, among others:

Anti-virus with sandboxing and machine learning
Effective defense against malware and viruses is ensured by the firewall, which reliably detects suspicious files.
To protect against as-yet unknown threats (zero-day exploits), suspicious files are first loaded into a protected cloud. In this isolated sandbox environment, the files can be securely and reliably tested.
Analyses using third-generation machine learning based on billions of samples allows scanning and proactive blocking of threats based on their behavior.
The cloud is hosted in Germany and complies with European data-protection policy.

SSL inspection: Security guaranteed even with encrypted channels
Data-traffic encryption is increasingly widespread and, although this is welcome from the secrecy point of view, there is the risk that malware can enter the systems via encrypted channels.
Thanks to SSL inspection, even encrypted data packets can be scanned and filtered, applications detected, and security requirements successfully implemented.
The UTM firewall becomes a trusted “man-in-the-middle” in communication, for example between a client and a web server.

Deep packet inspection: Detailed filtering and validation of applications and protocols
Deep Packet Inspection (DPI) protects against cyber attacks by precisely classifying the network traffic, protocols and applications, and it protects against data leaks.
In contrast to Stateful Packet Inspection, which only checks the meta-data (header) of the data packets, DPI checks down to layer 7, i.e. the packet data itself. In this way, data packets are checked for viruses, spam and other undesirable content.
Furthermore, detailed security policies actively regulate the use of certain applications, such as streaming services or browsers.

IDS / IPS: database-oriented protection against threats
The Intrusion Detection / Prevention System (IDS / IPS) maintains a database of known threats in order to protect the endpoints in the network from a wide range of hostile attacks, to issue warning messages in the event of an incident, and to terminate the communication link to hostile sources.
The underlying threat database contains a blacklist of IP addresses and detects patterns employed by malware in communication links, network scans, brute force attacks, and more.
While the IDS / IPS system in IDS mode only generates warning messages if a rule applies to the data traffic, in IPS mode the system additionally blocks malicious data traffic. Should a false alarm occur, the admin can allow the data traffic.

HTTP(S) proxy: Secure Web Gateway
The HTTP(S) proxy in the UTM firewall serves as a “middleman” for filtering and analyzing network traffic down to the application level in order to defend against Internet-based attacks.
Since this specifically concerns attacks from the Internet, we refer to a “Secure Web Gateway” (SWG).
When the Internet is accessed, the proxy connects to the web server, uses its own HTTP(S) proxy CA to generate a pseudo-certificate for the website, and uses this to connect to the browser.
As a Secure Web Gateway, the UTM firewall can use a proxy to analyze the data traffic, apply URL and content filters, and search for viruses.

Application management and content filter: full control over permitted applications and content
With the help of application management, admins themselves decide which applications should be allowed or blocked on the network.
In order to increase network performance, trusted applications can also be redirected straight to the Internet or to an external remote site by means of local breakouts.
A content filter also provides the option of defining category-based filter rules, for example for criminal, pornographic or violent content. The integrated official domain list of content harmful to minors from the "Bundeszentrale für Kinder- und Jugendmedienschutz" (Federal Review Board for Media Harmful to Minors), which is constantly updated, ensures that the protection of minors is also a top priority.
This provides reliable protection of business integrity.

VLAN: secure zoning of the network
Segment your systems by means of VLAN zoning.
By separating networks – for example the accounting network from the human resources network – unauthorized access to sensitive company data can be better restricted.
With VLANs (Virtual Local Area Networks), this separation is not on a physical but on a logical level. All Ethernet packets are given VLAN tags that determine the zone affiliation.
Which computers are allowed to communicate across zone boundaries, and under which circumstances, is controlled and monitored by the firewall.
The simple decision for more security
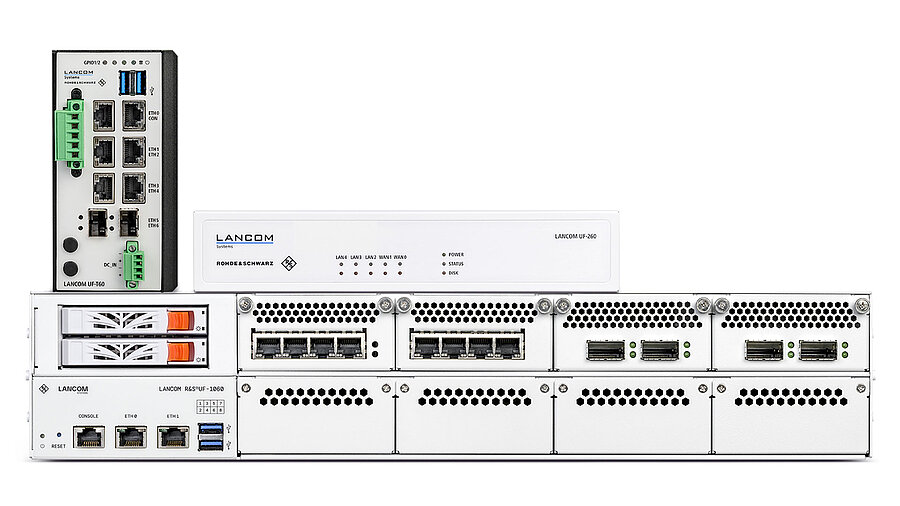
As you can see: Network security by means of Unified Threat Management is a complex matter. However, mastering it is not. The LANCOM R&S®Unified Firewalls are the first choice when it comes to manageable state-of-the-art IT security.
In combination with the LANCOM Management Cloud you benefit twice: You can enforce uniform security settings, secure passwords, and secure ports not only automatically, but at all locations too.
To the LANCOM R&S®Unified Firewalls product overview
Ask the AI chatbot!
Do you still have questions? Or maybe you cannot find the information you are looking for? The AI-based Digital Assistant will answer all your questions about network security, IT security, and LANCOM R&S®Unified Firewalls – at any time, quickly, and without searching! Alternatively, you can of course still use the contact form.