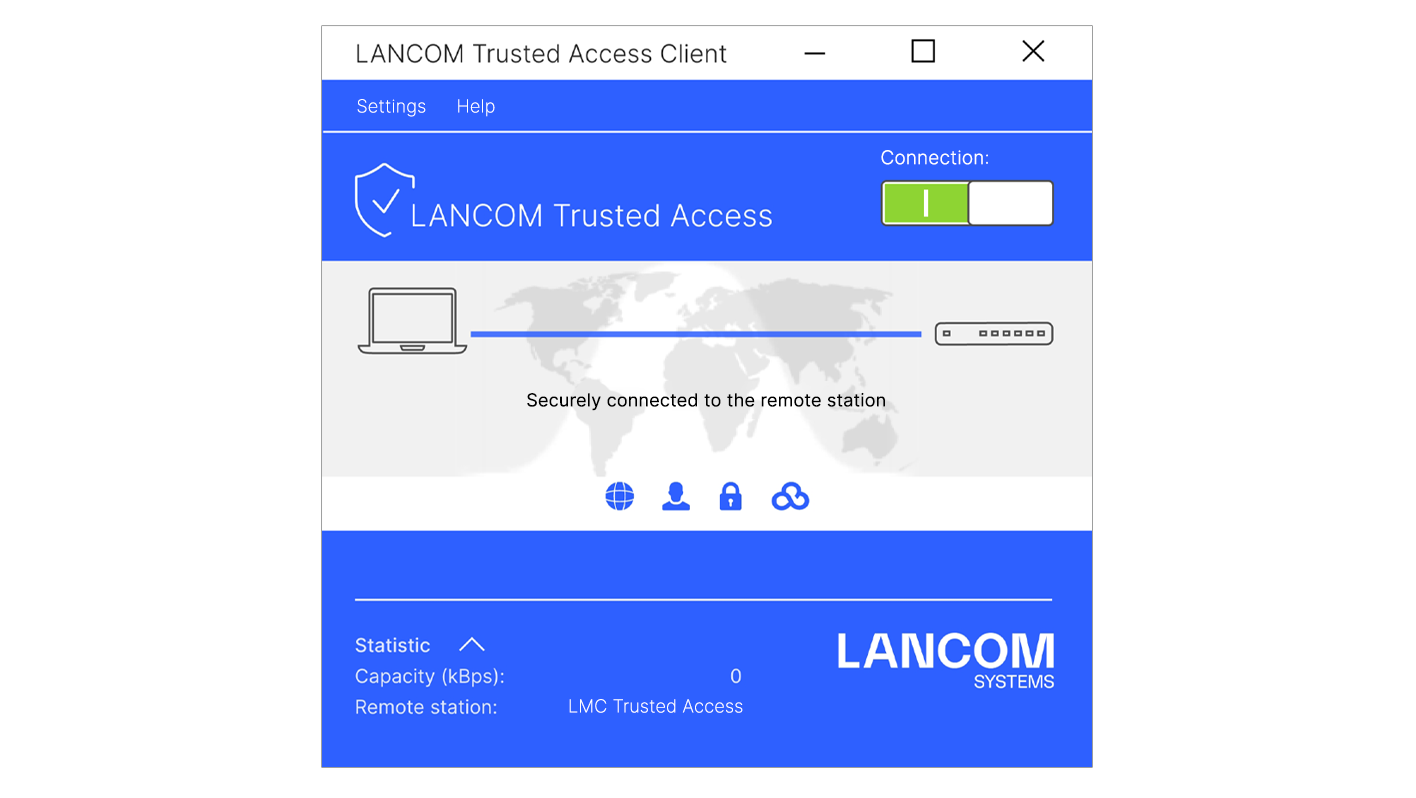
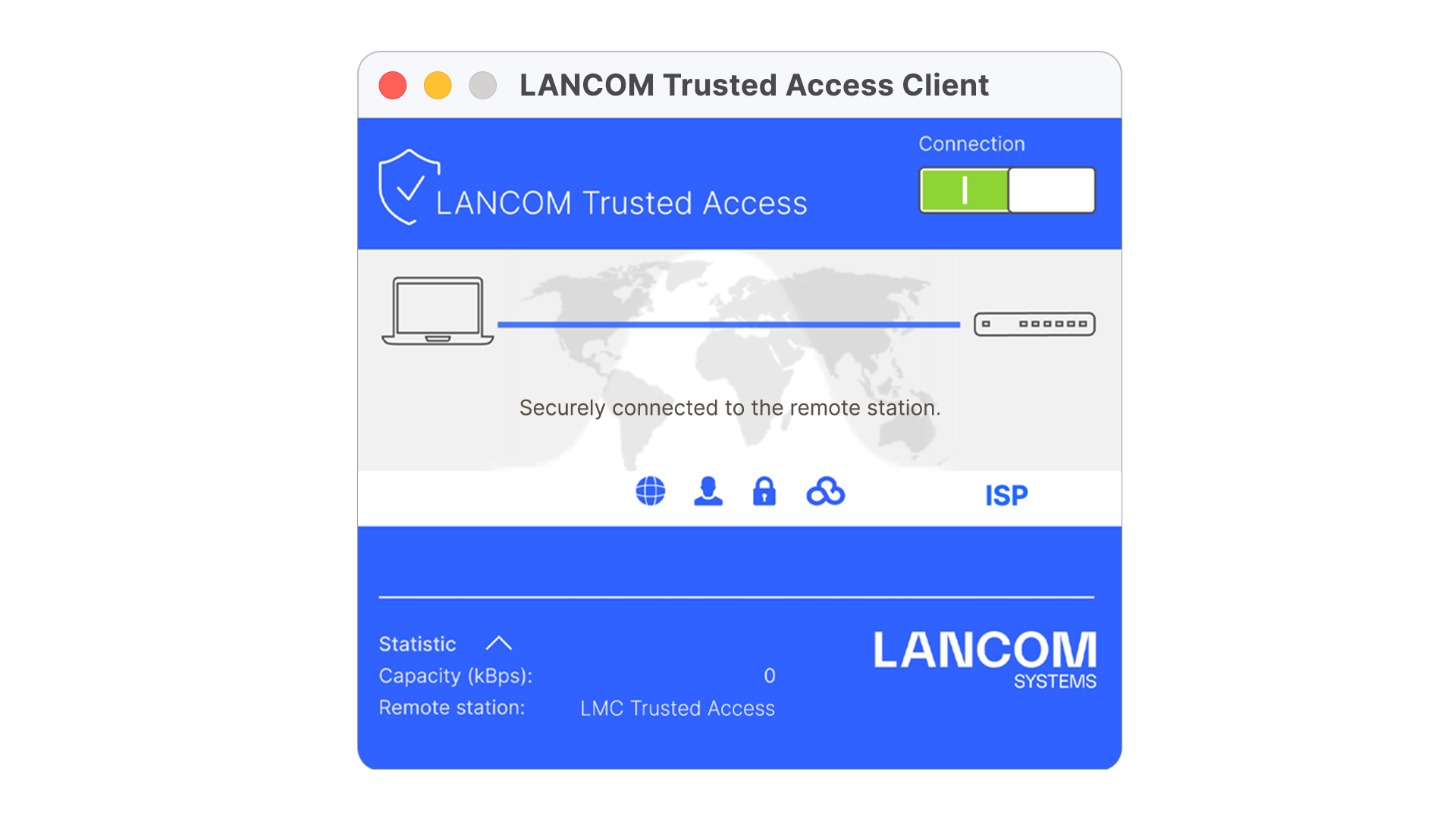
LANCOM Trusted Access Client (Windows & macOS)
LANCOM Trusted Access is the trusted network access security solution for enterprise networks. It enables secure and scalable access to enterprise applications for employees in the office, at home, or on the road, protecting modern hybrid working from anywhere, anytime. The LANCOM Trusted Access solution adapts to increasing security requirements in your organization and enables both cloud-managed VPN client networking for access to entire networks and the move to a Zero Trust security architecture for comprehensive network security. Based on granular access rights, users are only granted access to applications that have been assigned to them (Zero Trust principle). Existing systems for managing users and user groups (Active Directory) can be fully integrated into the LANCOM Management Cloud (LMC). For smaller networks, the LMC alternatively offers internal user management. LANCOM Trusted Access 100% GDPR compliant and scales for small businesses as well as for very large networks with several thousand users.
- Flexibly scalable secure network access solution for enterprise networks, that adapts to increasing security requirements
- Choice of granular access control to dedicated applications (Zero Trust principle) or entire networks (cloud-managed VPN client)
- Lateral protection from internal spread of malware in connection with micro-segmentation
- Migrates seamlessly into existing installations by integrating existing user databases in the company
- Endpoint security and multi-factor authentication for a high level of security
- Easy access to external cloud applications via single sign-on (SSO) without entering additional credentials
- Trusted Internet Access with Full Tunnel mode for mobile working as secure as in the office
- Full integration into the LANCOM Management Cloud (LMC) for zero-touch deployment and auto-configuration for easy and fast rollout of new remote access connections
- 100% GDPR compliant – data traffic runs without decoupling via an external cloud
Downloads for this product and usable LCOS versions can be found in our Download area.